CSP Allow-list Experiment
Tool: CSP Allow-list Experiment
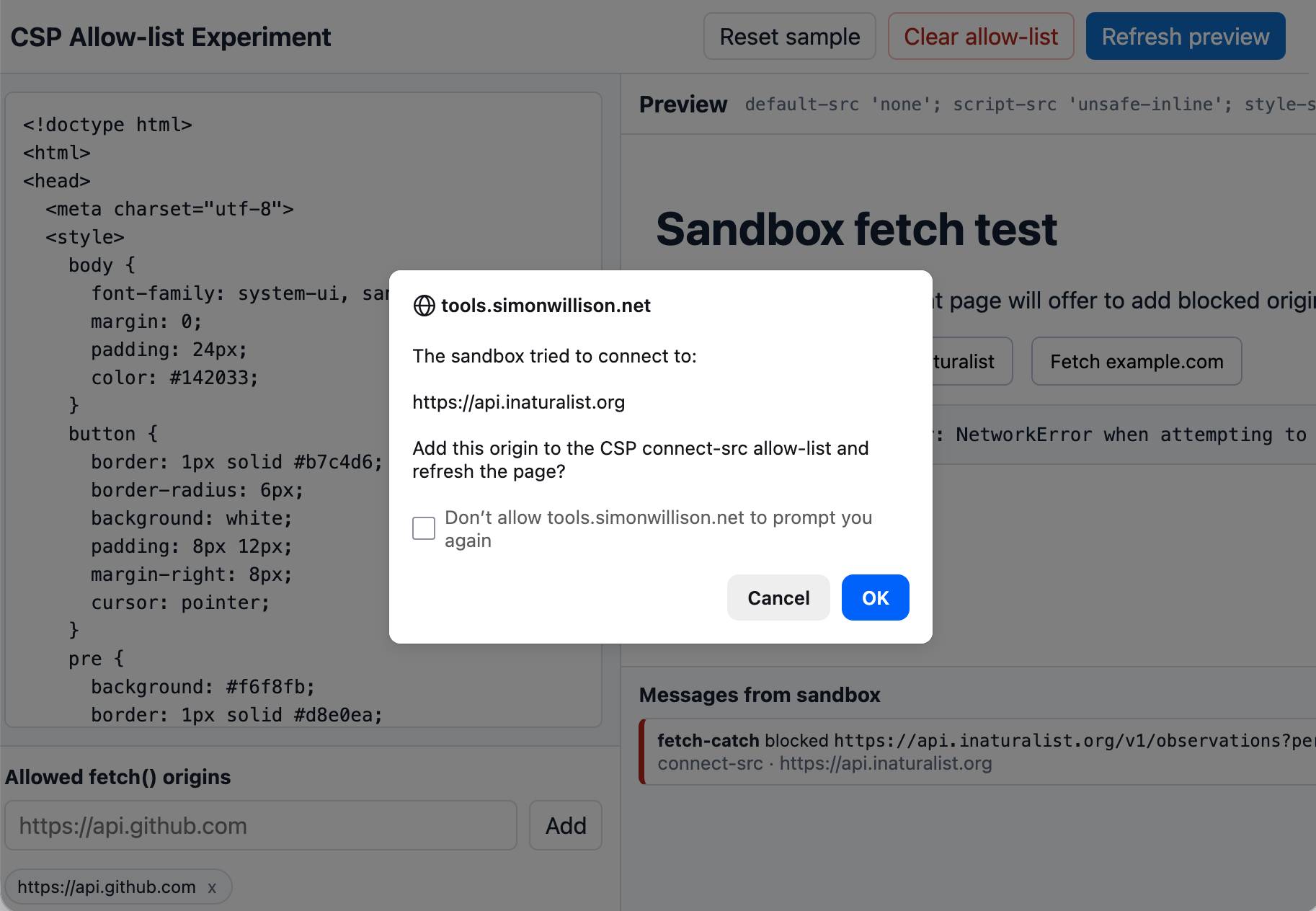
An experiment that shows that you can load an app in a CSP-protected sandboxed iframe (see previous note) and have a custom fetch() that intercepts CSP errors and passes them up to the parent window… which can then prompt the user to add that domain to an allow-list and then refresh the page.
I built this one with GPT-5.5 xhigh running in the Codex desktop app.
Tags: content-security-policy, iframes, security
Like
0
Liked
Liked